Hot Transmitter on 147.93 MHz Found and Shut Down
On the afternoon of October 10, a transmitter keyed up on 147.93 MHz. This happens to be the input frequency for club’s Grubstake VHF repeater (147.33/93). As a result, the repeater keyed up and eventually timed out. The offending transmitter never did time out over the course of three days. Unfortunately, this “hot transmitter” rendered the repeater unusable for service, and even resulted in the Thursday night ARES net being moved to the 30/90 repeater.
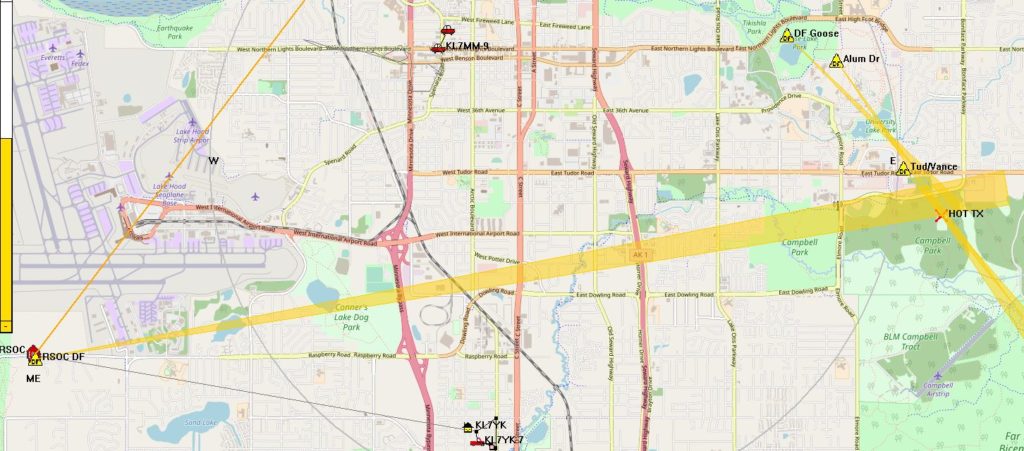
On October 11, we mustered an effort to find the source of the rogue transmission. I went to the RSOC and pulled a null bearing of 080 degrees on the log periodic. Shortly thereafter, Craig, KL4E, got busy with his Arrow antenna and Arrow attenuator. Between the two of us, we determined that the source was located somewhere in the vicinity of the Providence Hospital/UAA Campus area. Unfortunately, we both had to pack it in as we had other business to attend to.
Today, October 12, the transmitter was still going strong, so I got busy again. This time, I pulled out the 3-element tape measure beam antenna and Arrow attenuator (both loaned from John, KL7CY) and headed for the UMED District. Within a fairly short period of time, I found that the signal appeared to be coming from near the Southeast corner of the Alaska Native Medical Center campus. I continued to move and take bearings, and determined the signal was actually emanating from the south of Tudor Road. Also noted was that the signal was getting much stronger as I moved to the southeast as I needed to crank in more attenuation to get good bearings.
At this point, it was pretty clear that the source was either at the State of Alaska Crime Lab on the north side of Martin Luther King (MLK) Drive, or at the State of Alaska microwave tower site to the south of MLK drive. A quick check from the driveway access to the microwave site confirmed the signal was still to the southeast, so down the driveway I went.
There is a 100’ freestanding tower at the site just west of the microwave tower. The signal was huge right there, and there was no ability to attenuate it, even by completely removing the antenna and shielding the radio with my body. It was clear that I was at ground zero.

I contacted Greg Eubank, KL7EB as this site is one that he deals with for the State of Alaska. When Greg arrived and accessed the “shack” at the base of the tower, we found that the desk microphone attached to the

Motorola transceiver had a loop of coaxial cable resting atop of it just enough to cause it to key the transmitter. The culprit was found and the problem was solved.
We used the APRSIS32 program to help “map” the bearings and actually broadcast those bearings over APRS. Anyone running APRSIS32, or similar APRS mapping application would have been able to see those “lines of bearings” or “LOBs”.
It so happens that we have indeed been looking at the possibility of acquiring both fixed and mobile DF units for the RSOC and our MTV or pickup. This “hot transmitter” incident highlighted a need for this, and if we had these active we probably would have tracked the offending RF emanator on day 1 in short order!
If you’d like to get involved and work to help with establishing a good DF capability on VHF and UHF, please drop us a line at info@kl7aa.net, at a Working Wednesday or Open Saturday, at a club meeting, or contact us by filling out the form below.
Thanks to all involved for helping to resolve this issue and remember to secure your equipment when not in use!
73,
Kent, KL5T
COMMENTS:
Error: Contact form not found.



